Account Takeover Fraud: How Does it Happen?
Account takeover attacks are not random. They follow a clear lifecycle that begins with harvesting, culminates in access, and ends with monetization. By understanding how account takeover fraud occurs, financial institutions can better prevent and detect it.
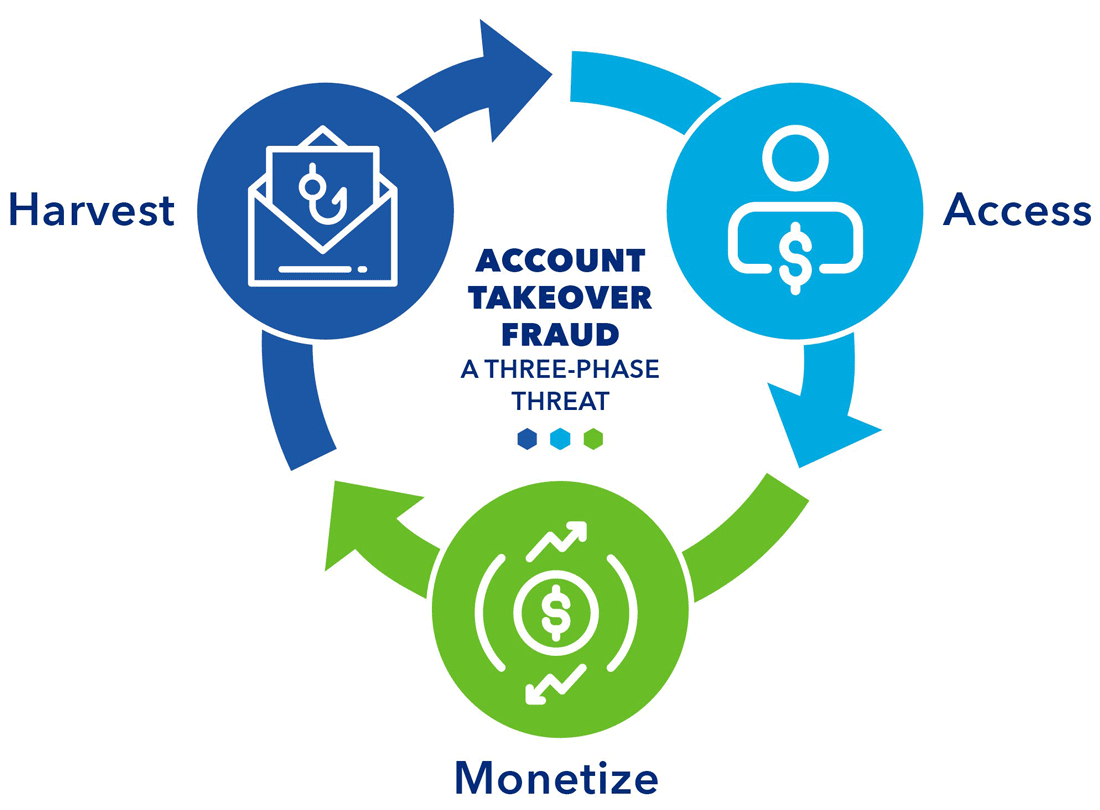
Harvest Phase: Storing and retrieving credentials and sensitive Personally Identifiable Information (PII).
Access Phase: Gaining entry, gathering intelligence and establishing control over victim accounts using automated tools, social engineering tactics, and strategic manipulation.
Monetize Phase: Seizing control and turning the account into a source of revenue.
For more details on each phase of the account takeover fraud lifecycle, watch the video below.
In this module, learn about:
Downloadable Resources
Explore these resources for additional information on how account takeover fraud happens.
| Document Title | Format | Reading Time |
|---|---|---|
| Understanding Account Takeover Fraud (PDF) | Document | 3 minutes |
| The Role of Non-Financial Digital Accounts in Account Takeover Fraud (PDF) | Document | 4 minutes |
| How Technology Is Driving Account Takeover Industrialization (PDF) | Document | 3 minutes |
| How Business Accounts May be Targeted for Account Takeover (PDF) | Document | 4 minutes |
| Infographic: Account Takeover Fraud Lifecycle (PDF) | Document | 4 minutes |
The account takeover fraud mitigation toolkit was developed by the Federal Reserve to help educate the industry about account takeover fraud and outline potential ways to help detect and mitigate this fraud type. Insights for this toolkit were provided through interviews with industry experts, publicly available research, and team member expertise. This toolkit is not intended to result in any regulatory or reporting requirements, imply any liabilities for fraud loss, or confer any legal status, legal definitions, or legal rights or responsibilities. While use of this toolkit throughout the industry is encouraged, utilization of the toolkit is voluntary at the discretion of each individual entity. Absent written consent, this toolkit may not be used in a manner that suggests the Federal Reserve endorses a third-party product or service.